![Exploiting Router with RouterSploit [Tutorial] Kali Linux | Welcome to Our channel Cyber Mafia CommanderX Official. We train you how to become a Powerful & Advanced Pentration Tester + Ethical Hacker. We Exploiting Router with RouterSploit [Tutorial] Kali Linux | Welcome to Our channel Cyber Mafia CommanderX Official. We train you how to become a Powerful & Advanced Pentration Tester + Ethical Hacker. We](https://lookaside.fbsbx.com/lookaside/crawler/media/?media_id=511033493215352&get_thumbnail=1)
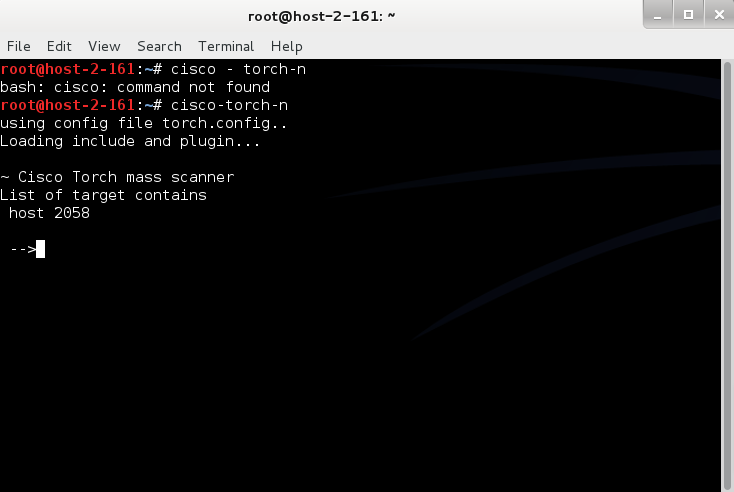
Exploiting Router with RouterSploit [Tutorial] Kali Linux | Welcome to Our channel Cyber Mafia CommanderX Official. We train you how to become a Powerful & Advanced Pentration Tester + Ethical Hacker. We

High-impact vulnerability in DrayTek routers leaves thousands of SMEs open to exploitation | The Daily Swig