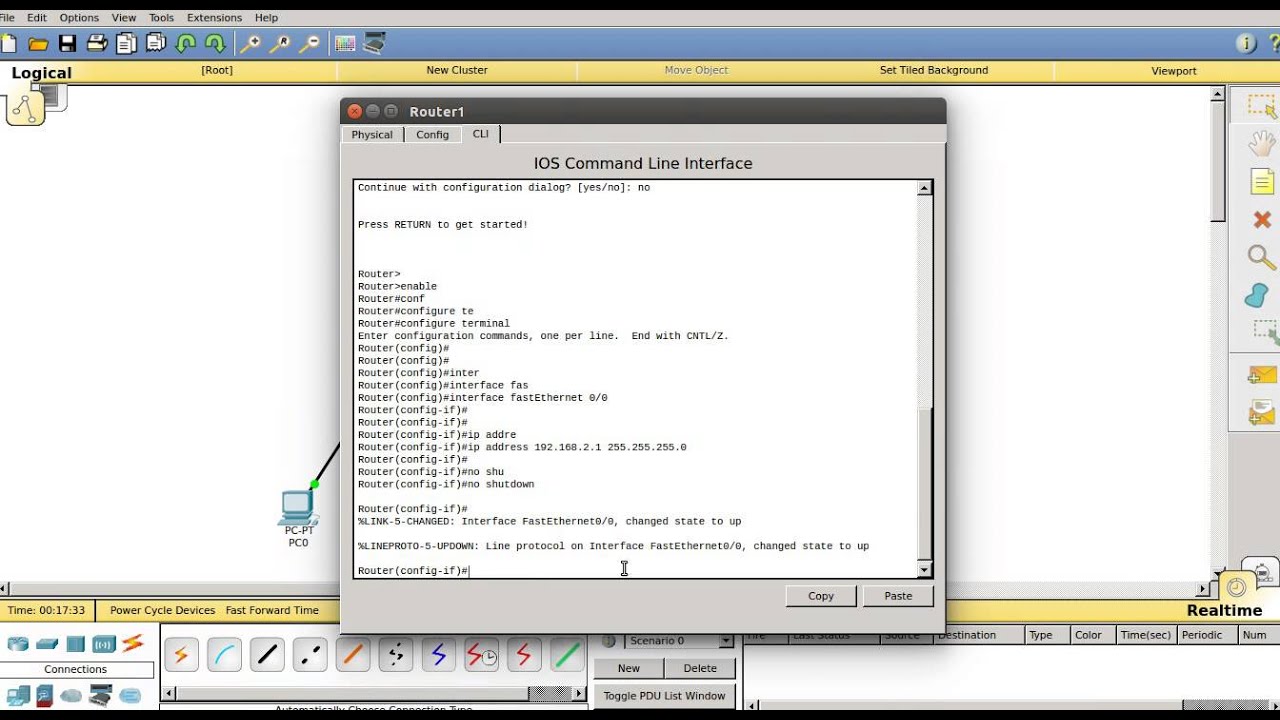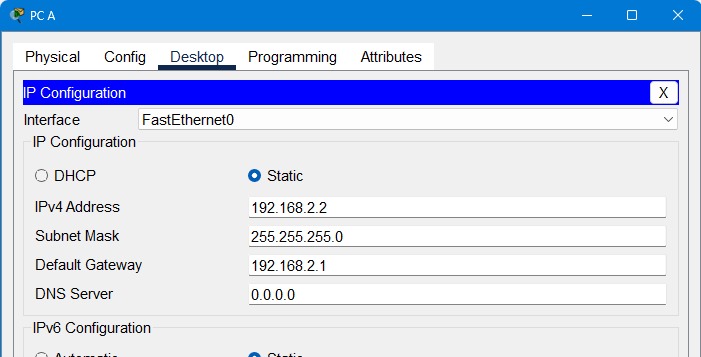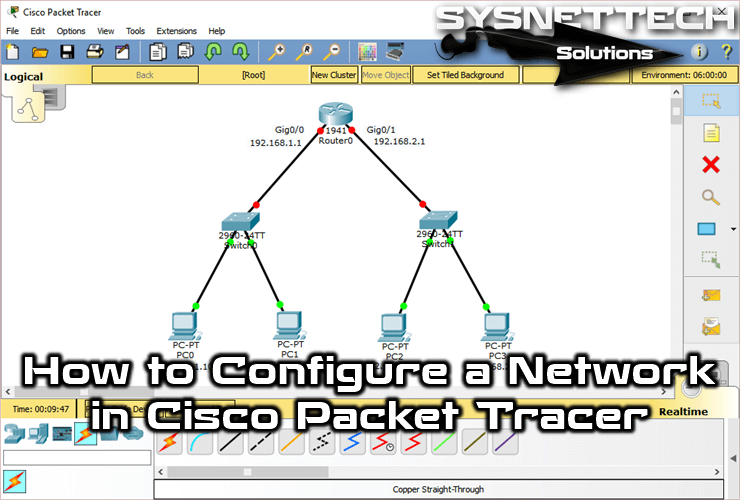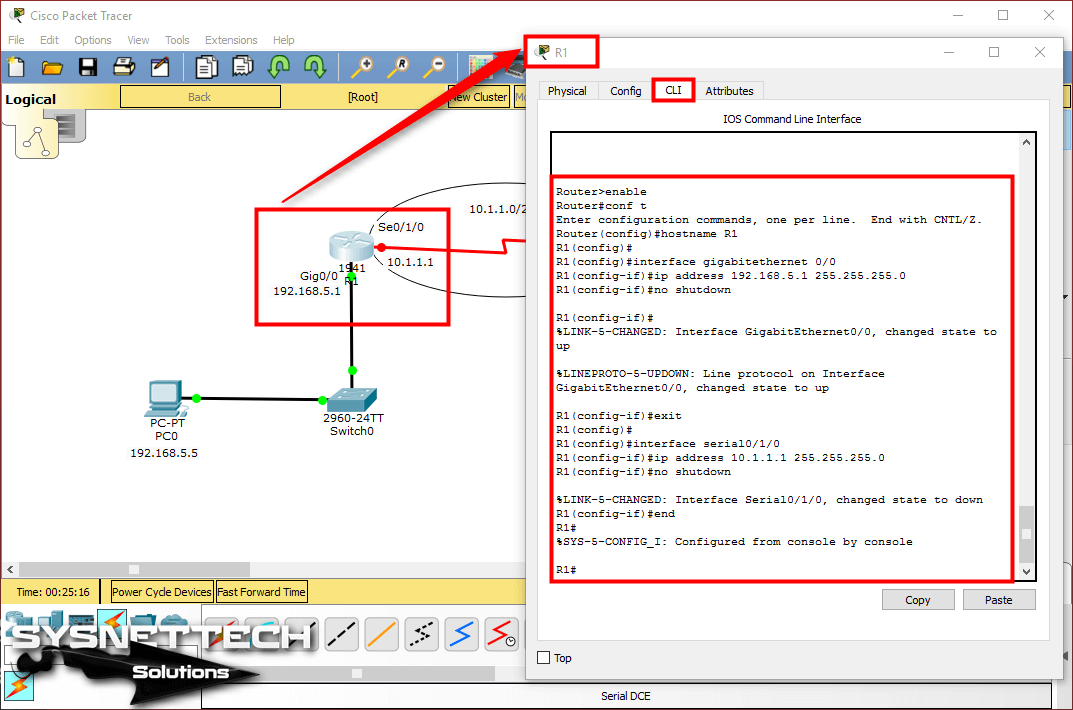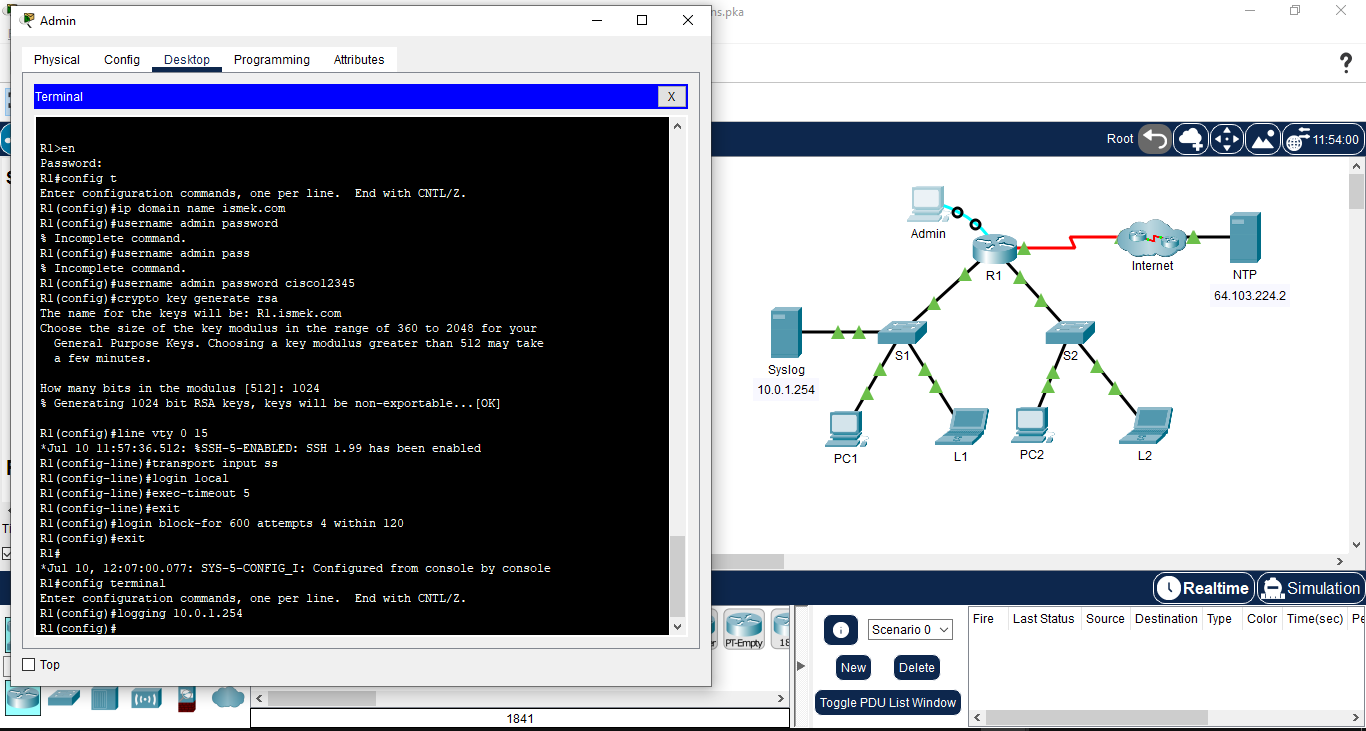
Using Packet Tracer to Configure Cisco Devices for Syslog, NTP, and SSH Operations | by Ahmet Talha Şen | System Weakness
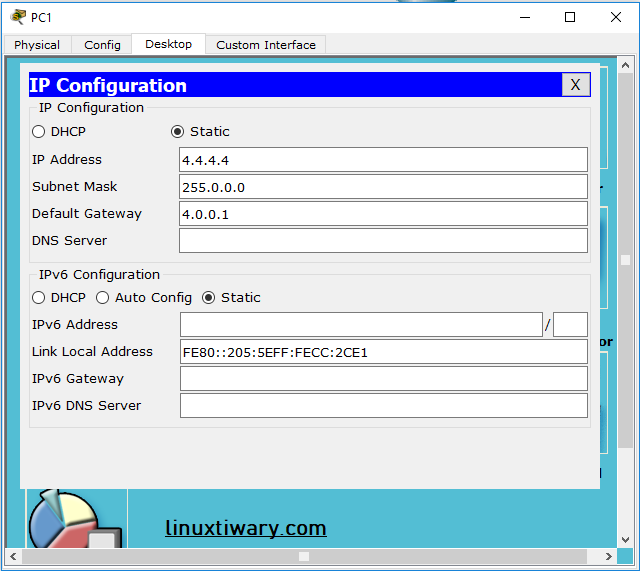
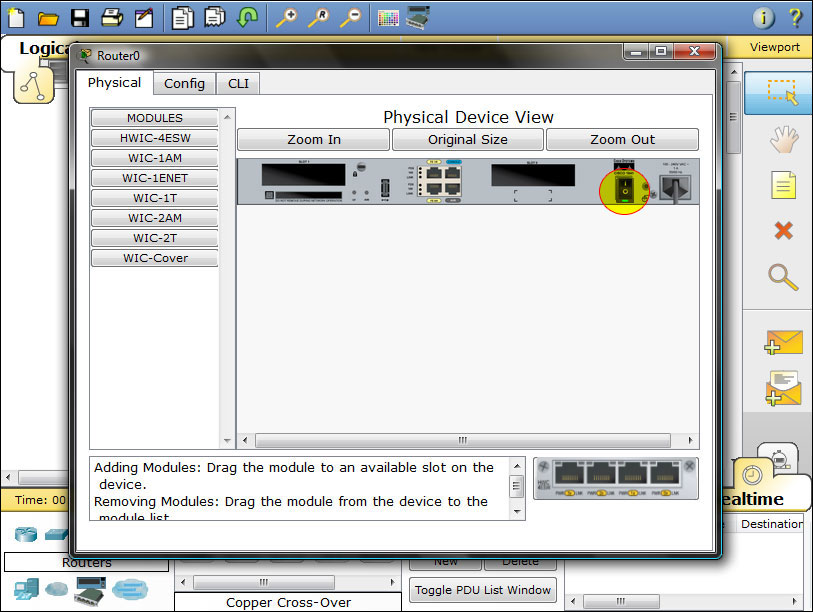
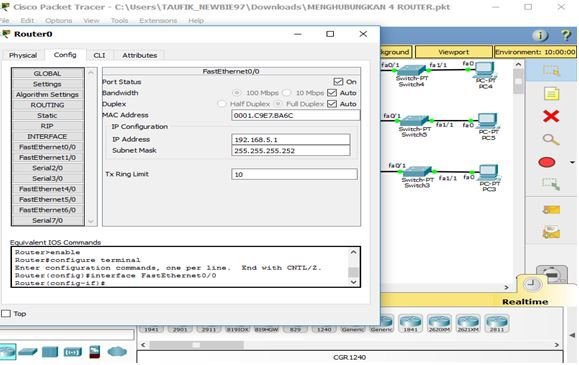
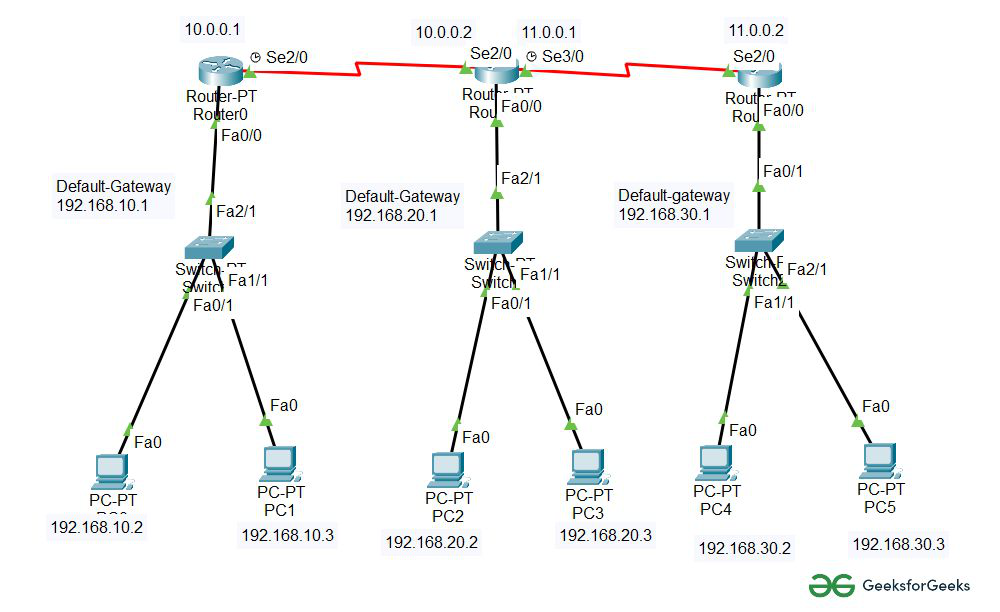
cisco packet tracer lab:configuring rip routing lab using two routers – Learn Linux CCNA CCNP CEH CISSP CISA Penetration-Testing Bug Bounty IPv6 Cyber-Security Network-Security Online